Feds charge 16 Russians allegedly tied to botnets used in cyberattacks and spying
The hacker ecosystem in Russia, more than perhaps anywhere else in the world, has long blurred…
The hacker ecosystem in Russia, more than perhaps anywhere else in the world, has long blurred…
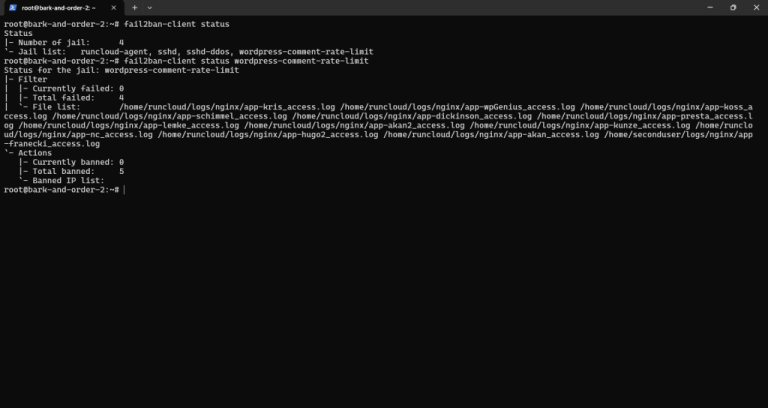
Is your website drowning in WordPress comment spam? If you’re battling endless waves of bot-generated junk,…
Welcome to Part 7 of the blog series on vSphere supervisor networking with NSX and AVI….

Biotechnology company Regeneron will acquire 23andMe out of bankruptcy for $256 million, with a plan to…
Keylogging, short for “keystroke logging” is the process of recording the keys struck on a keyboard,…
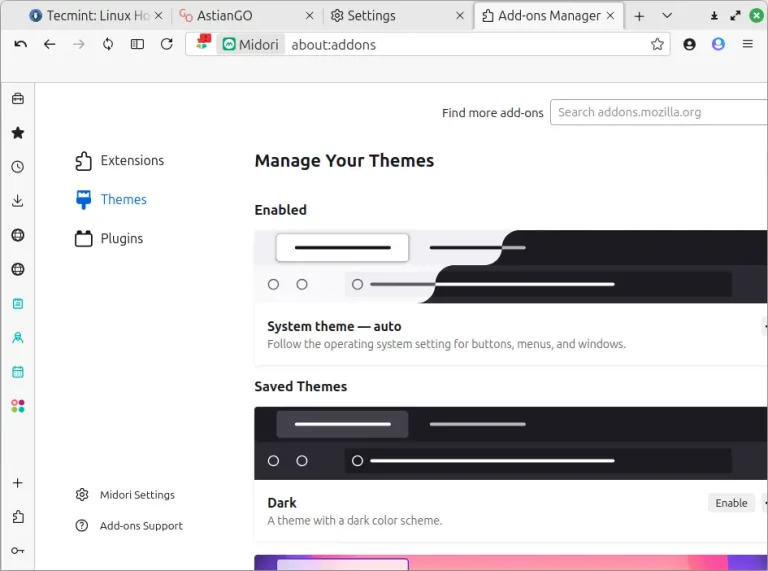
Midori is an open-source, lightweight, and fast web browser designed for people who want a simple…
Welcome back!!! Now that we activated vSphere supervisor in the previous article, let’s do few chapters…
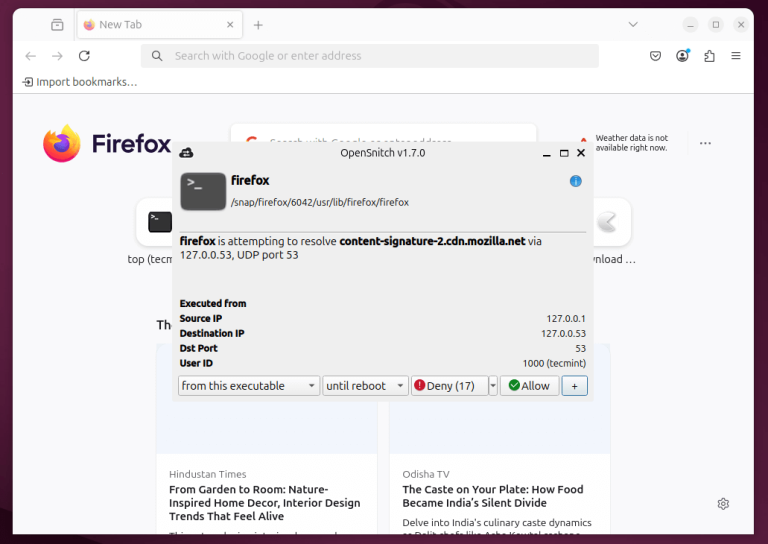
When it comes to protecting your Linux system from unwanted network connections, having a good firewall…

An interesting development has taken place as openSUSE has decided to not offer Deepin Desktop anymore…
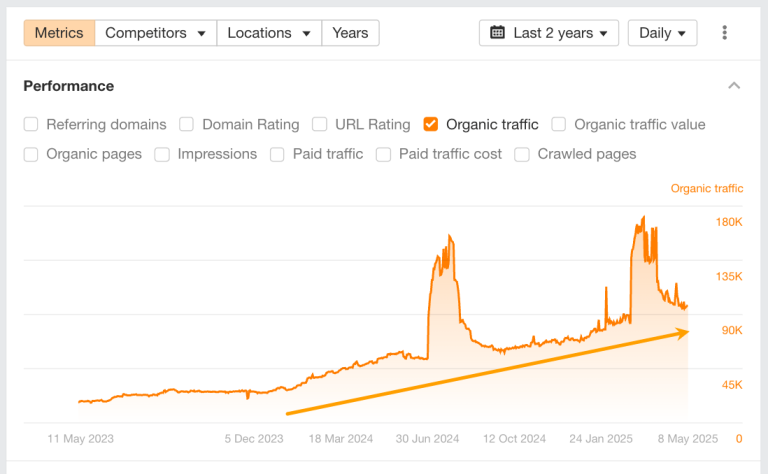
The cybersecurity industry is growing fast, with both new and established players competing for attention. Many…
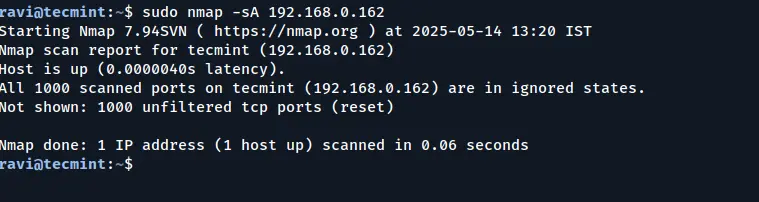
Nmap, short for Network Mapper, is an open-source and highly versatile tool used by Linux system…
Linux is one of the most widely used operating systems in both personal and enterprise environments….
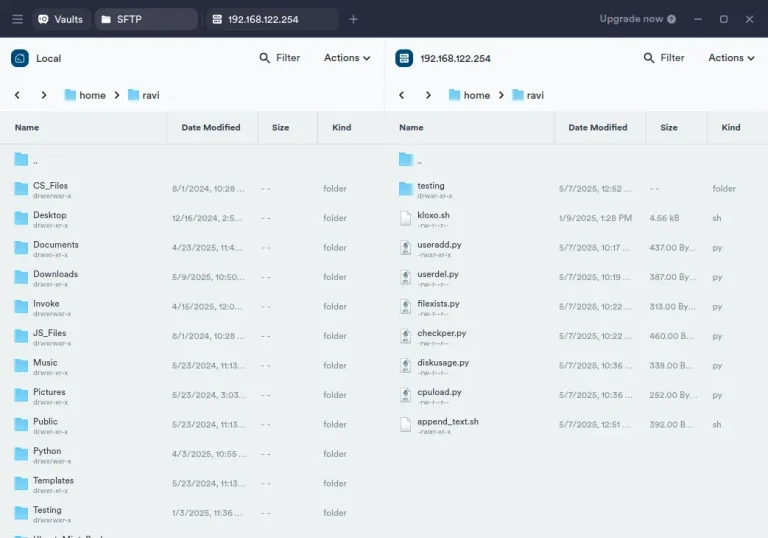
If you’re a Linux user, managing remote servers or networked devices via SSH (Secure Shell) is…

When setting up an Ubuntu server for production, securing the system is crucial to ensure its…
Rust everywhere! It was included in the Linux kernel code a couple of years ago. And…
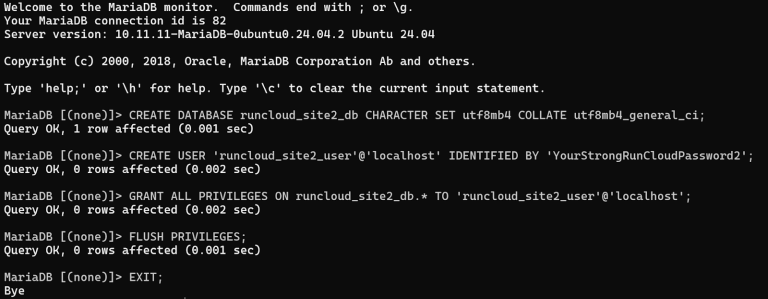
Most Ubuntu servers can handle far more than a single website. Hosting multiple sites on the…